Are you looking for the Answers to NPTEL Foundations of Cryptography Assignment 2? This article will help you with the answer to the National Programme on Technology Enhanced Learning (NPTEL) Course “ NPTEL Foundations of Cryptography Assignment 2 “
What is Foundations of Cryptography
The course provides the basic paradigm and principles of modern cryptography. The focus of this course will be on definitions and constructions of various cryptographic objects. We will try to understand what security properties are desirable in such objects, how to formally define these properties, and how to design objects that satisfy the definitions. The aim is that at the end of this course, the students are able to understand a significant portion of current cryptography research papers and standards.
CRITERIA TO GET A CERTIFICATE
Average assignment score = 25% of the average of best 8 assignments out of the total 12 assignments given in the course.
Exam score = 75% of the proctored certification exam score out of 100
Final score = Average assignment score + Exam score
YOU WILL BE ELIGIBLE FOR A CERTIFICATE ONLY IF THE AVERAGE ASSIGNMENT SCORE >=10/25 AND EXAM SCORE >= 30/75. If one of the 2 criteria is not met, you will not get the certificate even if the Final score >= 40/100.
Below you can find the answers for NPTEL Foundations of Cryptography Assignment 2
| Assignment No. | Answers |
|---|---|
| Foundations of Cryptography Assignment 1 | Click Here |
| Foundations of Cryptography Assignment 2 | Click Here |
| Foundations of Cryptography Assignment 3 | Click Here |
| Foundations of Cryptography Assignment 4 | Click Here |
NPTEL Foundations of Cryptography Assignment 2 Answers:-
Q1. Let G be a secure PRG. Then which of the following is not a secure PRG?

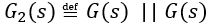

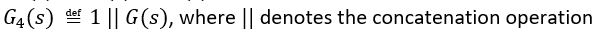
Answer:- a,b,c
Q2. Which of the following is(are) true about PRG?
a) A PRG is a deterministic algorithm
b) A PRG is a randomized algorithm
c) We can construct a PRG, which is secure against a computationally unbounded adversary
d) A computationally unbounded adversary can always determine the seed of a secure PRG, by seeing the output of the PRG
Answer:- a,d
Q3. Select the incorrect statement(s):
a) While using a PRG, same key can be used for every instance of encryption
b) If G(s) is a secure PRG, then G1 (s) ≝ G(s) || G(s+2) is also a secure PRG
Answer:- b
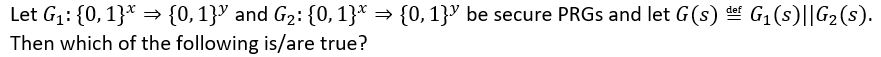
Q4.





Answer:- b,c
Q5.
a) Function G is a PRG
b) Function G is a true random number generator
c) Function G is not a PRG
Answer:- b
???? Next Week Answers: Assignment 03 ????
For other courses answers:- Visit
For Internship and job updates:- Visit
Disclaimer: We do not claim 100% surety of answers, these answers are based on our sole knowledge, and by posting these answers we are just trying to help students, so we urge do your assignment on your own.
if you have any suggestions then comment below or contact us at [email protected]
If you found this article Interesting and helpful, don’t forget to share it with your friends to get this information.